Reconnaissance is a common tactic to lay
Tag Archives: virus
The tactics of hackers have evolved over the past few years. As businesses wised up and deployed better data backup systems, hackers have changed their tactics to include a secondary means of extortion, namely, the threat to release exfiltrated data.
The Cybersecurity Threat Landscape continues to grow more ominous by the day. The year 2021 was peppered with several high-profile breach incidents. Perhaps more significant was the dramatic uptick in breach incidents that failed to make the evening news.
The warnings have been dire – YOU MUST UPGRADE TO WINDOWS 10! Is that really true? Are Microsoft, computer manufacturers, and computer resellers just making it all up? Let’s rewind a bit. Every operating system has an expiration date. After many stays of execution, Windows XP was finally dropped from support in June of 2014. […]
Windows 7 has been a very successful operating system since its release on October 22nd, 2009. Most users skipped over Windows 8 and Windows 8.1, finding Windows 7 to be trustworthy and reliable. But after a great 10-year run, Microsoft is calling it quits and support for Windows 7 is nearing the end. Everyone needs […]
Yahoo email has experienced yet another security breach by hackers. Should you be worried about this? Even if you do not currently have a Yahoo email address, it is my opinion that you still need to be concerned. Email account hacking has been a recurring theme for Yahoo in recent years and the timing couldn’t be worse. Yahoo has […]
Is it Time to Outsource Your Computer Support? Many businesses are beginning to reach that conclusion. “prevention is better than cure” -Erasmus Setting up a small business computer network used to be a relatively simple affair. A small business owner merely needed a few computers, an internet connection with a cable or DSL modem, some […]
More information has been trickling out regarding the massive Target PCI breach that took place during the 2013 Christmas shopping season. Forensic researchers first learned that hackers penetrated Target’s network by means of a business transaction portal. It appears that Fazio Mechanical Services was the source. Fazio is a Pittsburgh-area nationwide mechanical contractor that services […]
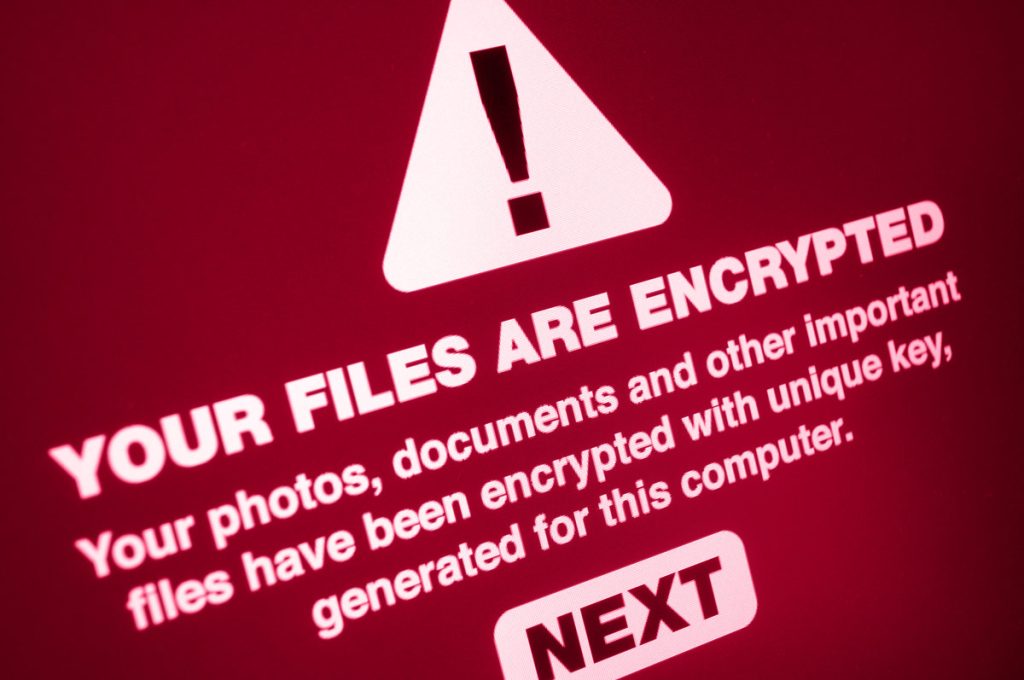
The “CryptoLocker” virus has been making a great deal of noise lately. Though we at Thom Infotech have not personally encountered it, we know others who have. We’ve written this post to help you to understand and defend against the CryptoLocker virus. What is it? CryptoLocker is an insidious twist on the all-too-familiar virus or […]
As of this writing there are roughly four useble business weeks left in the current year. As 2013 winds down, businesses should consider performing needed upgrades sooner rather than later. At the risk of creating a lengthy blog post I’m planning to provide 179 reasons to upgrade before January 2014. First, we should discuss the […]