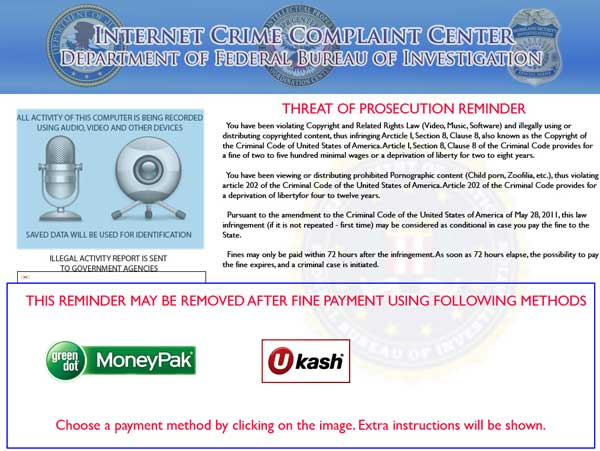
For crying out loud… How did this happen? You’re just surfing along, minding your own business and BAM – some bogus-looking thing pops up claiming you have 300 infected files and you need to pay $70 to get your computer cleaned. Or, like my elderly neighbor over the past weekend, you get a scary full-screen warning informing you that you’ll be prosecuted for copyright infringement. Here’s what that looked like…
My neighbor actually called the state police and the FBI about that one! So how did this happen, you ask? You have antivirus software – why didn’t it work? Well… antivirus software is good, but it’s no longer good enough. I’ll do my best to describe the process in layman’s terms.
“Malware” (malicious software) is a term that’s synonymous with the term “Virus”. There’s really no difference. The point of malware is for the bad guys to get their malicious software installed on your computer. It’s usually a scam to separate you from your money, but it can also include tools to steal your passwords and other sensitive information. The perpetrators are typically in Eastern Europe, though they could be anywhere.
So how does this happen? In nearly every case, the path to infection is through unpatched software on your computer. Software is notoriously buggy, and the bad guys are good at finding those bugs and leveraging them in order to grant themselves the right to install malicious software on your computer. For this reason it’s very important to keep your software patched (or updated). The most common “gateways” to your computer are programs that interact with your web browser such as Java, Adobe Flash Player, and Adobe Acrobat. Because these programs (and others like them) include browser plugins, the infection generally gets in when you merely visit an infected website. The site will have a few obscure lines of code that take advantage of the unpatched software and begin the malicious stuff. Your antivirus software literally sits there and watches it happen. If you’re lucky, it’ll tell you you’ve been infected – after the fact.
So how do you prevent this? First and foremost, always be sure to install patches when the respective vendors indicate they’re available. Adobe Acrobat can be configured to do this automatically. Flash Player now defaults this way as well. Java warns you, but nobody clicks that little orange coffee cup in the system tray (down by the clock) and does their updates. Frankly, if you are not specifically relying on Java you should just uninstall it (along with every other version of Java listed in “Add and Remove Programs” or “Programs and Features”). It’s just a matter of time before the current “safe” version (Release 7, Update 11 as of this writing) is found to have another fatal flaw. Do yourself a favor and get rid of it. You can always put it back later if you need it. Microsoft also prompts for updates to its software. The regularly scheduled patch day is every second Tuesday of the month (“Patch Tuesday”). Every now and then Microsoft releases an “out of band” patch for something critical that’s actively being exploited and can’t wait until next patch Tuesday. As a matter of fact, they did exactly that earlier this week. Thankfully, Microsoft has gotten pretty good at defaulting your computer to install the patches and reboot automatically. This is good, but if you shut down or use the “Sleep” or “Suspend” feature every day, chances are you’re behind on your patches. Stop reading this and do your patches now!
In any case, you need to be careful about how you get tricked into visiting the infected websites in the first place. The primary mechanism is an email that appears to come from FedEx, Amazon, your bank, or the like. The email looks very real, but hover your mouse over the links in the email and you’ll probably see some very bizarre-looking URL’s. Google searches are another good source – especially about current events. Lindsay Lohan’s latest exploits are profoundly interesting and the bad guys know this. They’ll create infected Lindsay Lohan websites hoping you’ll find them as you seek to increase your knowledge on the latest societal trends. Facebook is also a great breeding ground for links to infected sites.
A disturbing trend is the dreaded “zero-day” exploit.
